🔐 Data Destruction – Frequently Asked Questions
How is my data destroyed?
All data is erased using dedicated standalone hardware erasure systems, not consumer software.
Depending on the type of storage device, we use industry-recognised sanitisation methods in line with standards such as NIST SP 800-88 Rev.1 and legacy DoD guidance where appropriate.
For modern solid-state drives (including NVMe SSDs), data is removed at the drive controller level using secure erase and sanitisation commands designed specifically for flash storage. For traditional hard drives and SATA SSDs, controlled overwrite methods are used.
Once completed successfully, the original data is permanently unrecoverable by commercial or forensic means.
Is software wiping really secure?
When performed correctly, secure erasure can be effective — however, we do not rely on consumer-grade software or operating-system-based wiping tools.
Instead, we use purpose-built hardware erasure devices that operate independently of a computer, reduce the risk of user error, and provide verified results and reporting.
This approach is commonly used by organisations where data security and accountability are critical, including:
Banks and financial institutions
Government bodies
Enterprise IT and data centres
Managed service providers
Can data be recovered after a secure erase?
No — not in any realistic or practical sense.
Once a drive has been successfully sanitised using approved methods aligned with NIST SP 800-88, the data is considered permanently destroyed and cannot be recovered by commercial data recovery services or forensic techniques.
Any attempt at recovery would require extraordinary resources and is considered infeasible under recognised data-protection standards.
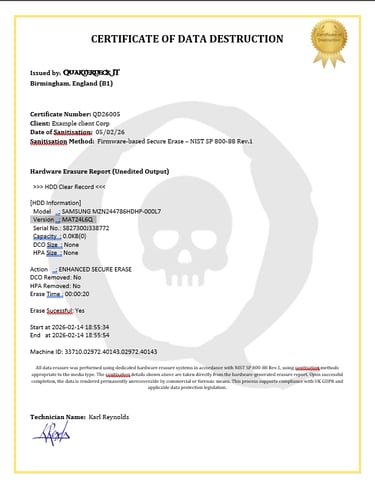
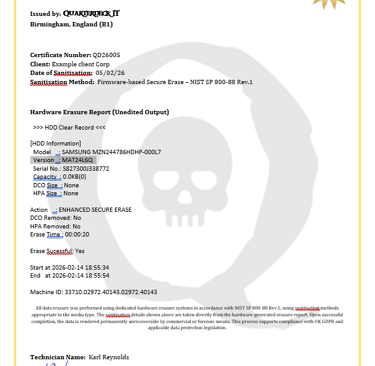
What proof do I receive?
For every batch of equipment processed, we issue a Certificate of Data Destruction, which includes:
Device serial numbers
Drive type
Erasure method used
Date and time of erasure
Successful completion status
This provides a clear audit trail suitable for GDPR compliance, cyber-insurance requirements, and internal records.
Is this GDPR compliant?
Yes.
UK GDPR requires organisations to ensure that personal and sensitive data is disposed of securely and that the process can be demonstrated.
Our erasure process provides:
Secure and appropriate data removal
Documented evidence of destruction
Clear accountability
This satisfies GDPR, ICO, and general data-protection obligations.
What happens to equipment after wiping?
Once data has been securely removed, equipment may be:
Refurbished and reused
Responsibly recycled
This approach reduces environmental impact while maintaining strict data security.
Who is this service for?
We provide secure data destruction for:
Small and medium-sized businesses
IT providers
Accountants and solicitors
Schools and charities
Home users
If a device has stored personal, financial, or confidential information, it should always be securely wiped before disposal or reuse.
Why choose Quarterdeck IT?
Because we provide:
Industry-recognised erasure standards
Verified results and audit reporting
Responsible reuse and recycling
A local, accountable service
You don’t just get your data destroyed — you get proof that it was done properly.